The ADVYON 2026 Hurricane Readiness Checklist…
General
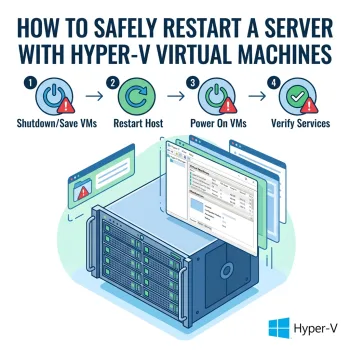
How to Safely Restart a Server with Hyper-V Virtual Machines
Restarting a physical server that hosts Hyper-V virtual machines requires careful preparation. Restarting without properly shutting down virtual machines and Hyper-V services can cause long shutdown delays, frozen services, or even virtual machine corruption. This support article outlines a safe, repeatable process for restarting a Hyper-V host server with minimal risk and downtime. Purpose To safely restart a physical server hosting Hyper-V virtual machines without causing service interruptions, shutdown hangs, or extended reboot times. Scope…
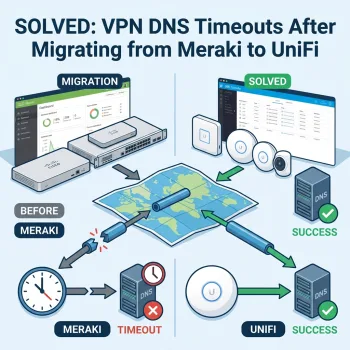
SOLVED: VPN DNS Timeouts After Migrating from Meraki to UniFi
How to Fix Domain Join and DNS Issues Over a Site-to-Site VPN If you recently migrated from Cisco Meraki to Ubiquiti UniFi and your VPN shows “connected” but DNS and domain services fail, you’re not alone. This is a common issue when replacing Meraki AutoVPN with standard UniFi IPsec tunnels. In this guide, we’ll explain: Why DNS fails over VPN even when the tunnel is up Why TCP works but UDP times out The exact…
SharePoint: The Dos and Don’ts of Sharing Files
SharePoint is a robust file server that helps organizations store and manage files efficiently. However, with great functionality comes the responsibility of ensuring it’s used securely. Here are some best practices and important considerations when sharing files through SharePoint: Be Cautious About Allowing Access When granting access to your SharePoint site, it’s essential to carefully control who gets in—especially when dealing with external users. Understand the Risks of Improper Settings If sharing settings…
Windows Defender Scam
The Windows Defender Browser Pop Up scam is a deceptive tactic where a fake alert appears on your web browser, claiming to be from Windows Defender. It usually warns about a virus infection or security issue on your computer, prompting you to take immediate action. However, it’s a trick designed to scare users into clicking on malicious links, downloading harmful software, or providing personal information. Windows Defender, the legitimate antivirus program for Windows, doesn’t display…
8 Reasons Your Internet May Be Slow, And How To Fix It
Resolving a slow internet connection is typically achievable if the issue lies on your end, but the solution varies based on the underlying cause. Speed bottlenecks may stem from factors like a sluggish internet plan, Wi-Fi interference, or outdated equipment. Instead of spending an entire afternoon troubleshooting, we offer a quicker solution. Our compiled list details the eight most prevalent reasons for a slow internet connection, increasing the likelihood that one of these fixes will…
How to Enable Incognito Mode in Chrome for Windows and MacOS
Here is how to enable Incognito Mode in Chrome for both Windows and Mac OS X. What Is Incognito Mode? Incognito Mode in Chrome is Google’s implementation of private browsing. Users can activate this mode and surf the internet without Chrome recording any cookies, usernames, passwords, or history. This can be a concern for parents because it could allow children to view pornography or other inappropriate material without leaving behind any traces. Incognito Mode in…
What to Do After a Cyberattack
Written By Tibby Fielding If your organization experiences a cyberattack, it is vital to react quickly and immediately enable your incident response plan. Your response plan should include the following tasks which help ensure the incident is suppressed to reduce a loss in data. You will need to access and contain the attack, remove the threat, restore data and services, report the incident, and revise your incident response plan. Read the following to…
Are you getting pop ups when composing or replying to emails in Gmail?
Written By Ian Britten and Tibby Fielding Are you receiving this pop up when composing or replying via Gmail? This pop up is occurring because your Gmail signature contains images that have been copied and pasted into the signature. To fix this issue, you can insert image files into your signature. If you do not have the image files, there is an easy way to download them. (Skip to Step 3 if you already have the…
How to check for files that did not sync in Dropbox
To check which files did not sync in dropbox, they may show up in the Bad Files Check. Click the link below and sign in to find them. https://www.dropbox.com/bad_files_check…