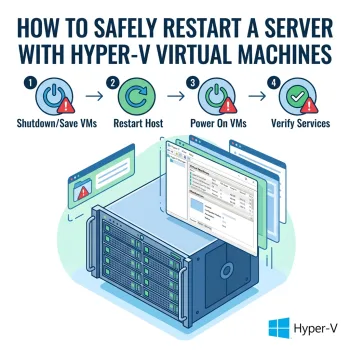
Restarting a physical server that hosts Hyper-V virtual machines requires careful preparation. Restarting without properly shutting down virtual machines and Hyper-V services can cause long shutdown delays, frozen services, or even virtual machine corruption. This support article outlines a safe, repeatable process for restarting a Hyper-V host server with minimal risk and downtime. Purpose To safely restart a physical server hosting Hyper-V virtual machines without causing service interruptions, shutdown hangs, or extended reboot times. Scope…
Support Articles
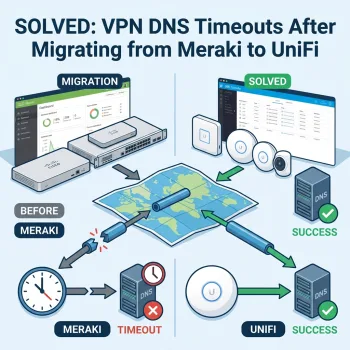
SOLVED: VPN DNS Timeouts After Migrating from Meraki to UniFi
How to Fix Domain Join and DNS Issues Over a Site-to-Site VPN If you recently migrated from Cisco Meraki to Ubiquiti UniFi and your VPN shows “connected” but DNS and domain services fail, you’re not alone. This is a common issue when replacing Meraki AutoVPN with standard UniFi IPsec tunnels. In this guide, we’ll explain: Why DNS fails over VPN even when the tunnel is up Why TCP works but UDP times out The exact…
Security Alert: Beware of DeepSeek AI App!
In today’s digital world, connectivity is the foundation of any successful business.
Missing Web Office 365 Onedrive & Sharepoint Apps
Are you or your 365 tenants experiencing issues with your Office 365, OneDrive, or Sharepoint app icons not displaying in the top left corner menu of office.com? You can see here how the Sharepoint icon is missing for example for this tenant. The fix is easy and all it requires is for you to have access to an 365 admin account on your…
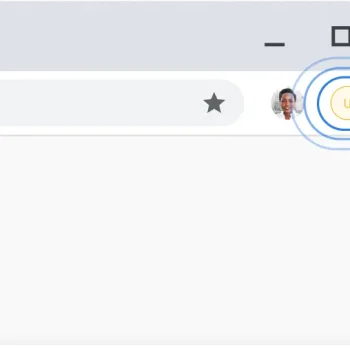
How to Update Chrome
1. Open Chrome 2. In upper right corner, click on the three dots: 3. Towards the bottom of the list choose “Settings” 4. From the list on the left side, select “About Chrome” 5. Updates will automatically begin, if not, select “Update Google Chrome” 6. Click “Relaunch” once updates are completed to optimize Chrome…
Launch Quickbooks in Multi-User Mode
There are 2 ways to launch a Quickbooks file into Multi-User Mode. Important: First make sure that no one else has the Quickbooks file open or else you will not be able to launch it into Multi-User Mode. Method 1: Default Company file Launch Quickbooks and open up the company file like normal. 2. Click on File on…
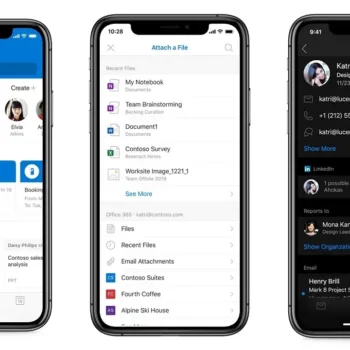
Outlook Mobile App for iOS and Android FAQs
Where do I download the Outlook mobile app? For Android: -Open the Google Play Store on your Android device. -In the search bar, type “Microsoft Outlook” and press Enter. -Look for the official Outlook app by Microsoft Corporation. -Tap on the app, and then tap “Install.” *If you are already on your mobile device, click the following…
Resolving issues regarding TPM error Office Signin Fix Solved
Sometimes after some changes are made to an account such as switching the account to a local account from a “live” account an error can occur where Office tries to re-authenticate the account as it is not sure what has occurred. Trying to sign in will trigger an error that will not allow the sign in due to TPM Failure. Your computer’s Trusted Platform Module has malfunctioned. There are a couple methods that you can…
Recovering OneDrive Deleted Files
Accidentally deleting a file or saving over a file that you needed the previous version of can happen to anyone. Thankfully those who take advantage of Microsoft’s OneDrive are able to recover said file or previous versions of files if it has not been 30 days since deletion/changes made. Recovering deleted files: 1. Go to office.com and click sign in. Use the…
What is SentinelOne?
With the increasing sophistication of cyber threats, companies in Summerville and Charleston, SC, need robust solutions to protect their sensitive data and ensure the smooth functioning of their operations. One such powerful ally in the realm of cybersecurity is SentinelOne. Understanding SentinelOne: SentinelOne is a cutting-edge cybersecurity platform that offers comprehensive protection against a wide range of cyber threats, including malware, ransomware, and other malicious activities. Its innovative approach combines artificial intelligence, machine learning, and…